Incident response answers the immediate question. Forensics answers the important one.
When an incident is contained, the real work begins. Organisations face regulatory reporting deadlines, board-level questions, legal obligations, and the need to understand the full scope of what occurred. Gut feeling and logs are not enough — you need evidence.
Our Digital Forensics & Incident Investigation service deploys experienced investigators to reconstruct exactly what happened: how attackers entered, how far they moved, what they accessed or exfiltrated, and when. We produce findings that hold up to scrutiny — from your regulator, your insurer, and your board.
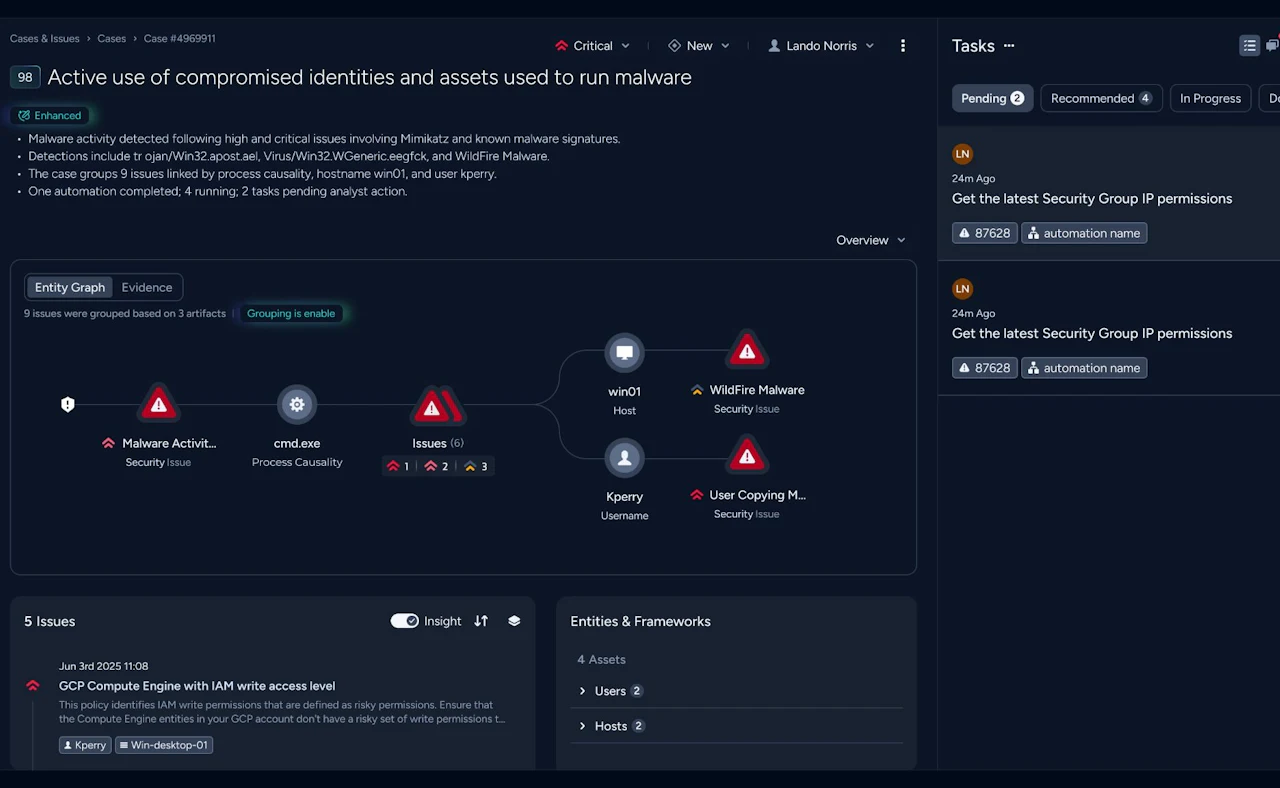
Preservation and analysis of compromised endpoints, servers, and cloud environments using forensically sound collection methods. Evidence integrity maintained throughout.
Correlation of log sources, artefacts, and system evidence to produce a verified chronological account of attacker activity — from initial access to detection.
Static and dynamic analysis of malicious files and tooling recovered during investigation — establishing attacker capability, intent, and indicators for detection.
Structured evidence packages prepared to the standards required for regulatory notification, legal proceedings, or cyber insurance claims.
Clear, factual reporting that translates technical findings into plain-language conclusions for senior leadership and supervisory authorities.
Targeted remediation recommendations based on verified attacker paths — closing the specific gaps exploited, not a generic security checklist.
What makes our forensics capability credible
Investigators, not generalists
- Digital forensics requires specific skills that are different from incident response or penetration testing. Our investigators are trained in forensic evidence handling, artefact analysis, and the evidentiary standards required when findings need to withstand legal and regulatory scrutiny.
Evidence integrity from the first call
- Forensic investigations are undermined by poor collection practice — overwritten artefacts, broken chain of custody, tainted evidence. We apply forensically sound procedures from the moment we are engaged, regardless of how early in an incident that is.
NIS2 and DORA reporting fluency
- European regulatory notification requirements are specific about what incident reports must contain and when they must be submitted. We understand these obligations and structure our investigation output to support compliant reporting — not generic findings that leave your compliance team to do the translation.
Investigation that leads to remediation
- A forensic report that ends with findings and no path forward leaves your organisation exposed. Because Nomios also delivers security engineering and managed services, our investigation conclusions connect directly to teams who can close the gaps — on your environment, not a generic recommendation list.
When the incident is over, the questions begin. We help you answer them.
Talk to our team about how a forensic investigation engagement works — and how quickly we can be on-site when you need us.