Why one partner across all domains matters
A circle of trust is one of the oldest and most human concepts in security — the idea that you share what matters most only with those you know, those who are capable, and those who will not let you down. It is built slowly, through demonstrated reliability and shared experience. And once established, it is the foundation on which everything else rests.
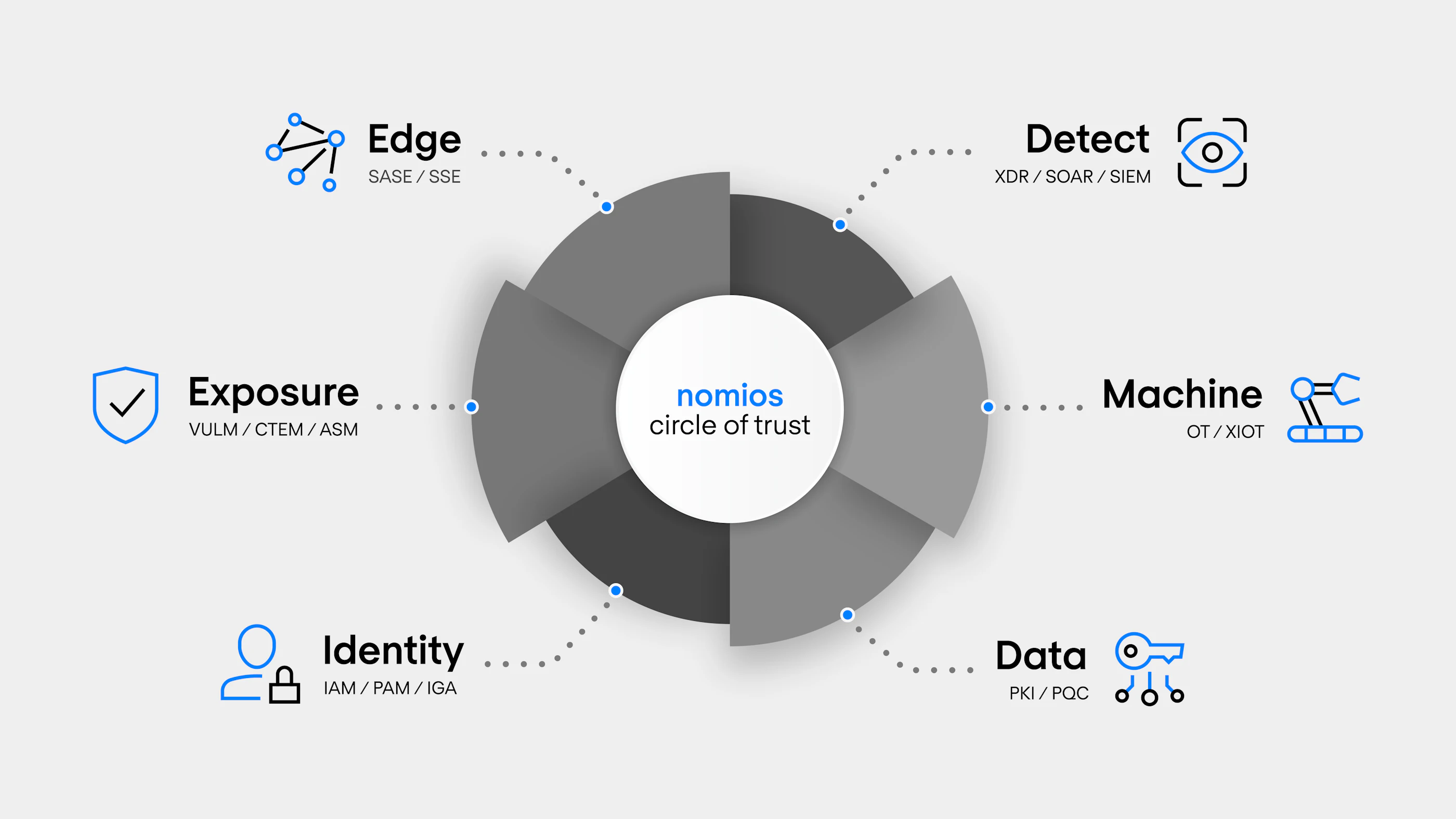
That is exactly what Nomios aims to be for our clients. Not a vendor relationship — a trusted partnership across every dimension of your security programme. One organisation you can bring your hardest problems to, knowing we have the expertise to help, the independence to be honest, and the track record to back it up.
Cybersecurity is not a collection of independent problems. A vulnerability discovered in the exposure domain should inform detection rules. An identity compromise should trigger network response. A data breach has implications for governance and compliance. When these domains are handled by different suppliers, the connections between them are missed — and attackers exploit exactly those gaps. Nomios is one of the few MSSPs in Europe with genuine, deep expertise across all domains — built through decades of delivery, strategic acquisitions, and a deliberate commitment to breadth without sacrificing depth.
- Secure access from anywhere — connecting users, devices, and applications without trusting the network they are on.
- 24/7 threat detection and response — finding attackers before they reach their objective, and containing them when they do.
- Continuous visibility into your attack surface — finding, prioritising, and closing the vulnerabilities that matter before they are exploited.
- Controlling who has access to what — governing digital identities across workforce, privileged users, and the systems they touch.
- Protecting the operational technology and connected devices that run critical infrastructure — where availability and safety are as important as confidentiality.
- Protecting data at the cryptographic layer — so that even when systems are compromised, the data they hold remains secure.
Edge
Detect
Exposure
Identity
Machine
Data
"Few MSSPs in Europe can honestly say they have deep expertise across all of these domains. Nomios can."
Built through decades of delivery, specialist acquisitions, and a deliberate refusal to be a one-trick vendor — the Nomios Circle of Trust is the foundation of a security partnership that grows with your organisation, not one that runs out of capability when your needs evolve.

Edge & Access
Users work from everywhere. Applications live in the cloud. The network perimeter has dissolved. The Edge & Access domain is where Nomios helps organisations take back control — securing access from any user, any device, any location, to any application.

Detection & Response
Detection and response is not a product — it is an operational discipline. Nomios brings together the intelligence, technology, and human expertise to detect threats earlier, investigate faster, and respond decisively — before attackers reach their objective.

Exposure Management
Exposure Management is the discipline of continuously understanding what is visible, what is exploitable, and what needs to be fixed first — across your entire attack surface. Nomios delivers that capability across every dimension of your environment.
Industrial & OT Security
Operational technology, industrial control systems, and connected machines power the infrastructure that keeps society running. As IT and OT converge, protecting these environments requires expertise that goes far beyond conventional cybersecurity — and Nomios delivers it.
Identity security
In a world without fixed boundaries, controlling who has access to what — and ensuring that access is appropriate, monitored, and protected — is the foundation of modern security. Nomios helps you build that foundation.
Data-centric security & encryption
Perimeters fail. Credentials get stolen. Networks get compromised. The organisations that recover fastest are those who protected their data at the source — with cryptography, key management, and certificate infrastructure that holds even when everything else doesn't.
Ready to explore what a complete security partnership looks like?
Talk to our team in The Netherlands about your environment — and where the gaps in your current approach are.