Most organisations have some playbooks. Very few have the right ones.
Generic incident response playbooks — drafted once, filed away, never tested — offer the appearance of preparedness without the substance. The gap shows up the moment a real incident unfolds: procedures that do not match the actual environment, escalation paths that assume resources that do not exist, response steps written without consulting the people expected to follow them.
Playbook development and MITRE ATT&CK alignment are core disciplines within our managed detection and response service and SOC & SecOps practice. This page explains the methodology — because for CISOs building or maturing a security programme, understanding how detection and response capability is constructed matters as much as knowing it exists.
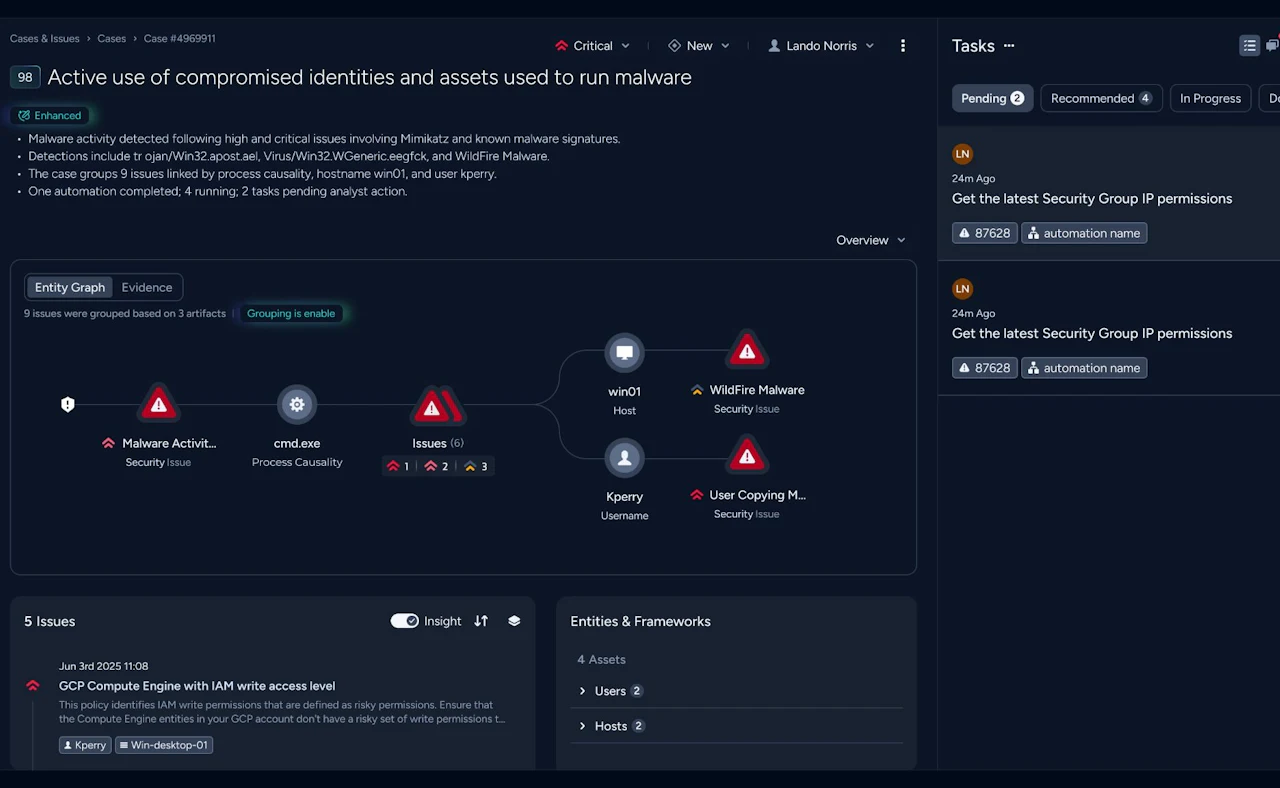
Playbooks built around specific incident types — ransomware, business email compromise, insider threat, supply chain compromise — that walk your team through investigation, containment, eradication, and recovery in sequence. Built for your environment, not a generic template.
- Scenario-specific, not one-size-fits-all
- Mapped to your actual tools, teams, and escalation paths
- Decision-tree format for high-pressure conditions
- Aligned to NIS2 notification timelines where relevant
Operational playbooks that govern how alerts are triaged, investigated, escalated, and closed — removing ambiguity from the SOC workflow and ensuring consistent quality of response regardless of who is on shift.
- Alert triage and severity classification
- Escalation criteria and communication procedures
- Containment actions by alert type
- Documentation and evidence preservation standards
Defence built around how adversaries actually behave
MITRE ATT&CK is a structured knowledge base of adversary tactics, techniques, and procedures observed in real attacks. We use it as the foundation for both detection engineering and playbook development — ensuring that what we build reflects real threat behaviour, not assumptions.
We map your current detection rules and playbooks against the ATT&CK framework to produce a clear picture of which techniques you can detect and respond to — and which are blind spots.
Not all techniques are equally relevant. We prioritise coverage gaps based on the threat groups and attack patterns most active against your sector and geography — focusing effort where it matters most.
Gaps become development targets. New detection use cases and playbooks are built to address the highest-priority uncovered techniques — and integrated into the live monitoring environment.
ATT&CK coverage is not a one-time exercise. As the threat landscape evolves and your environment changes, coverage is reviewed and updated — ensuring your defence keeps pace with the adversary.
ATT&CK alignment gives your CISO and board a structured, evidence-based way to understand detection maturity — not a subjective assessment, but a mapped view of what the programme can and cannot detect.
ATT&CK heatmaps and coverage summaries translate technical detection posture into a format that supports board-level security programme reporting and investment decisions.
What sound playbook and ATT&CK practice delivers
Faster, more consistent response under pressure
- When an incident unfolds, cognitive load is high and time is short. A well-designed, tested playbook removes the need to improvise decisions that should already be made — reducing response time and improving the consistency of actions taken regardless of who is handling the incident.
Detection that reflects real threats, not theoretical ones
- ATT&CK alignment ensures that detection investment is directed at techniques adversaries actually use against organisations like yours — not the techniques that are easiest to detect or that happened to come with the SIEM platform. Coverage gaps are visible, measurable, and addressable.
Regulatory readiness built into the response workflow
- NIS2 requires organisations to notify authorities within defined timeframes. DORA requires documented incident response procedures. Playbooks that incorporate these obligations — with named decision-makers and defined trigger criteria — make compliance a natural output of good incident handling, not a retrospective scramble.
A defensible security posture for the board
- ATT&CK coverage mapping gives CISOs a structured, evidence-based account of detection maturity. That is valuable both internally — for prioritising investment — and externally, when regulators, insurers, or boards ask how the organisation knows its defences are adequate.
How would your team perform if an incident started tonight?
Talk to our team about the state of your playbooks, your ATT&CK coverage, and what a structured improvement programme looks like within our managed detection & response service.