The NCSC recently published a practical guide for security professionals: Convince your board of assume breach. The core message is clear, but it calls for a shift in mindset that goes well beyond a policy document. Assume breach does not mean giving up. It means being realistic.
Attackers will get in — the question is what happens next
Traditional security strategies are largely built on prevention: firewalls, filters, access controls. Those measures are necessary, but not sufficient. Modern attackers bypass perimeters through stolen credentials, abuse of legitimate SaaS tools, or compromised supply chains. They move laterally through networks, accumulate privileges, and wait.
The average dwell time — the period between initial access and detection — still runs to tens of days in many environments. During that window, attackers can establish a firm foothold, exfiltrate data, or lay the groundwork for ransomware.
The NCSC therefore asks boards to ask different questions. Not just: are we protected? But: how quickly do we detect an attacker already inside — and how quickly can we contain them?
What assume breach means operationally
Assume breach is not a philosophy for the boardroom alone. It is a design principle for your detection and response capability.
In practice, it means:
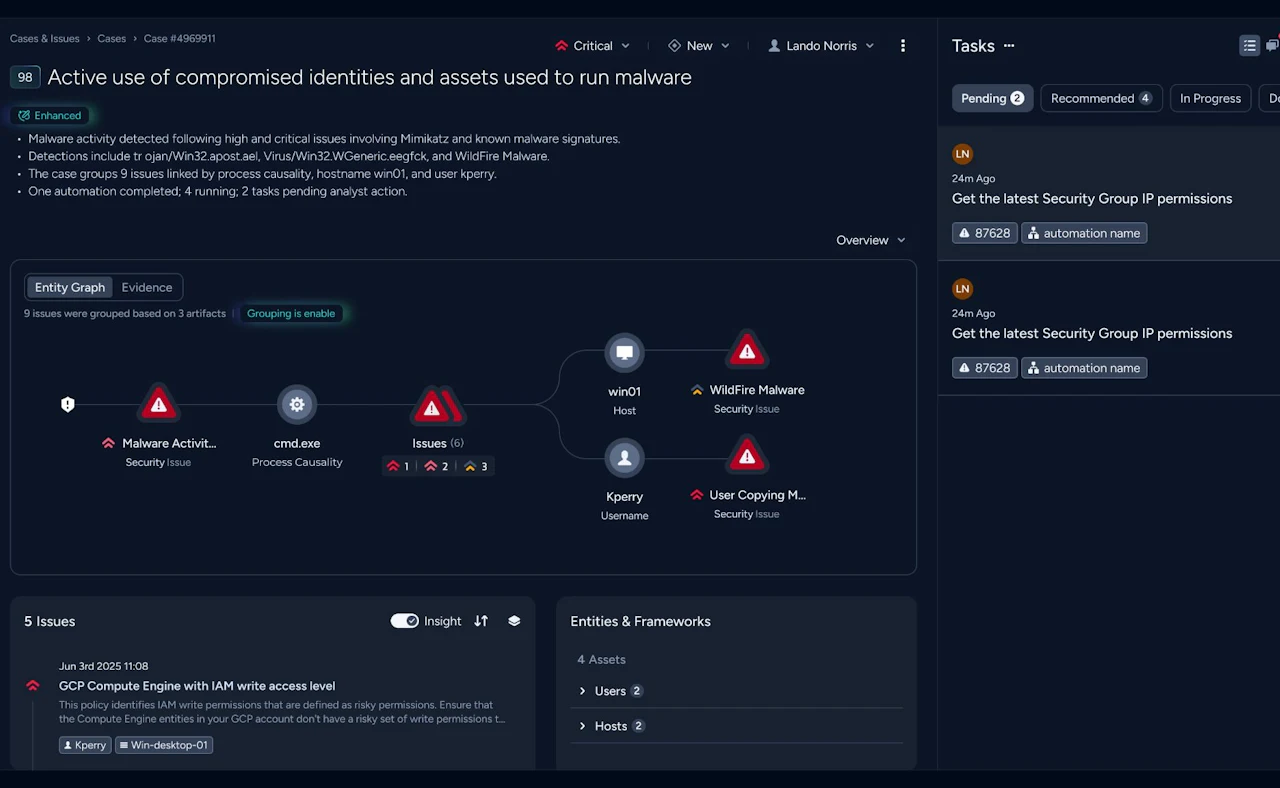
Detection after authentication. Attackers who have obtained valid credentials initially behave 'normally'. Detection requires visibility into behavioural patterns: unusual OAuth authorisations, token replay, anomalous service principal activity. These signals are not visible at the perimeter — they are visible in identity and network telemetry.
Lateral movement as an early warning signal. Attackers moving from system to system leave traces in protocols such as Kerberos, SMB, and RDP. Network Detection and Response (NDR) technology — such as that provided by Vectra AI — is specifically designed to detect this east-west movement, including within encrypted traffic. Without payload inspection, but based on traffic patterns and behavioural models.
Containment as the primary objective. Detection without rapid response has limited value. The second question the NCSC raises — how quickly can we contain? — requires automated or semi-automated containment capability: revoking sessions, isolating accounts, adjusting conditional access policies. And this in minutes, not hours.
Measurable resilience. Assume breach demands metrics that a board can understand: median dwell time, time-to-detect (MTTD), time-to-contain (MTTC). Not technical laundry lists, but trend lines that show whether the organisation is becoming more resilient over time.
The challenge for security teams
Most security teams understand the principle. The challenge lies in execution.
Assume breach requires continuous monitoring of identity, endpoint, and network telemetry — combined, not siloed. It requires runbooks fast enough to stay ahead of the attacker. And it requires reporting that bridges the gap between the SOC and the board.
That is a substantial operational undertaking, particularly for organisations without a mature in-house SOC or the tooling to bring all this telemetry together.
How Nomios MDR operationalises this
At Nomios, we work with organisations that want to translate the assume breach principle into concrete detection and response capability — not as a theoretical framework, but as day-to-day operations.
Our MDR service is specifically designed for post-compromise detection: continuous monitoring of identity misuse, lateral movement, and suspicious outbound traffic, combined with rapid containment playbooks across identity provider, endpoint, and network. Monthly reporting gives boards insight into MTTD, MTTC, and risk reduction over time — aligned with the NCSC's governance recommendations.
For organisations that want to understand where they stand today, we offer an Assume Breach Readiness Assessment: a two-week measurement of post-compromise exposure, with an actionable report as the outcome.
Our team is ready for you
Do you want to know more about this topic? Leave a message or your number and we'll call you back. We are looking forward to helping you further.