For years, cybersecurity has been built around a detect-and-respond model: monitor for threats, identify breaches, contain the damage. That model has served its purpose — but it is no longer sufficient on its own.
Preemptive security represents a fundamental shift in thinking. Rather than waiting for an attacker to make their move, organisations identify and close vulnerabilities before they can be exploited, disrupt threats before they materialise, and build resilience into their environment from the ground up.
Gartner predicts that by 2030, preemptive cybersecurity solutions will account for 50% of IT security spending — replacing traditional detection-and-response as the primary defence against cyber threats.
Why now
AI has changed the attack landscape in ways that make reactive security increasingly inadequate.
Attackers now use AI to generate convincing phishing campaigns at scale, discover and exploit vulnerabilities faster than most organisations can patch them, and adapt their tactics in real time to evade detection. The global attack surface — spanning multicloud environments, IoT devices, APIs, and an ever-growing range of connected systems — is expanding faster than it can be manually managed.
In this environment, the organisations most at risk are those still operating under the assumption that they will catch a breach after it happens. The window between a vulnerability being discovered and being exploited is shrinking. Detection-and-response alone cannot close that gap.
What preemptive security looks like in practice
Gartner frames preemptive cybersecurity around three principles: deny, deceive, and disrupt.
Deny — close the doors before attackers can find them. This means continuous exposure management: systematically identifying vulnerabilities across your entire environment and addressing them before they can be exploited. It also means reducing your visible attack surface — making assets harder to find and target in the first place.
Deceive — make your environment unpredictable. Techniques such as decoys, honeypots, and dynamic configuration changes divert attackers away from critical systems, waste their time and resources, and generate intelligence about their tactics and intentions.
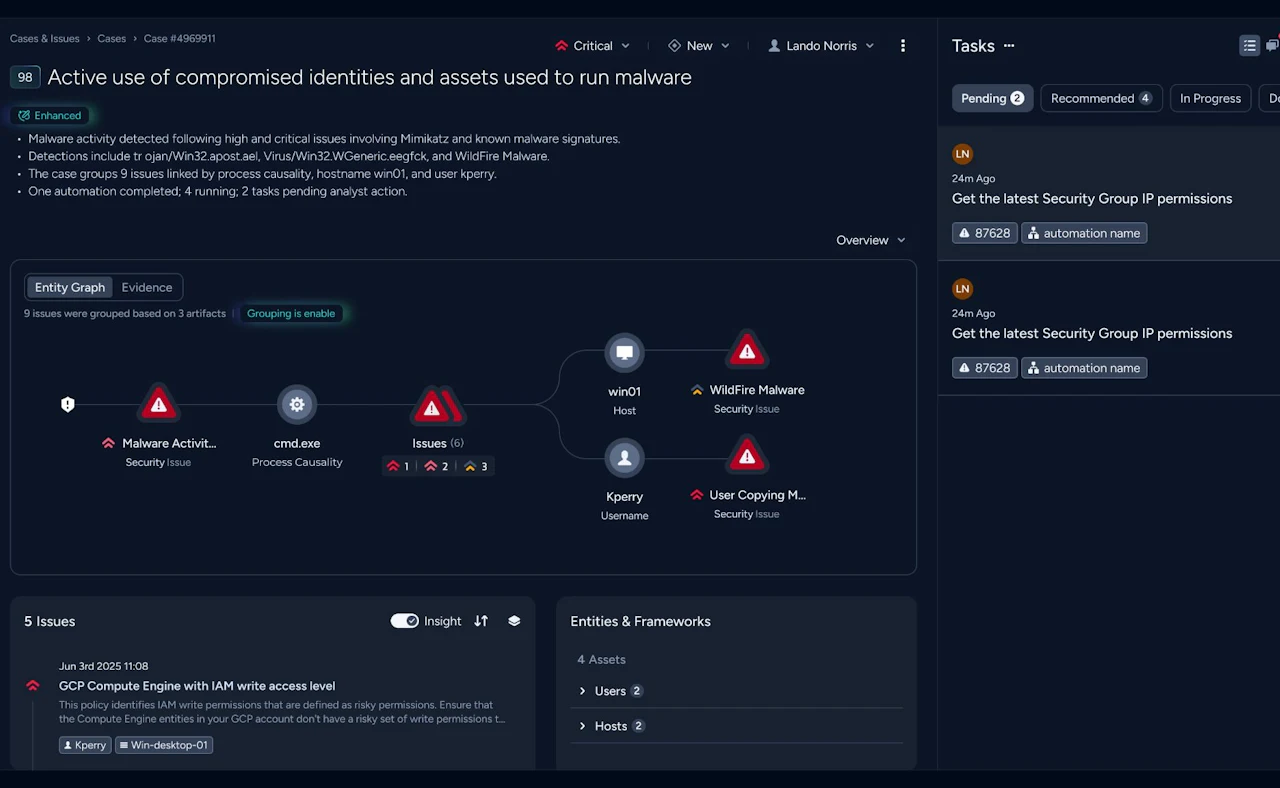
Disrupt — anticipate threats rather than react to them. Using predictive threat intelligence and automated monitoring, organisations can identify the precursors of an attack before it launches — and neutralise it before it causes disruption.
How Nomios helps
Nomios supports organisations in putting these principles into practice — combining technical expertise with a structured, evidence-based approach to preemptive security.
Penetration testing and red teaming We simulate real-world attacks to test how your defences hold up under pressure. Whether a targeted assessment of a specific system or a full-scope red team engagement, the goal is the same: find what an attacker would find, before they do.
Vulnerability management Continuous visibility into your vulnerabilities is the foundation of any preemptive security programme. We help organisations identify, prioritise, and systematically address weaknesses across their environment — ensuring that critical gaps don't go unnoticed or unresolved.
Security assessments A structured assessment of your security posture gives you an evidence-based picture of where you stand. We evaluate controls, configurations, and processes against recognised frameworks and real-world risk, and provide clear, actionable guidance on where to focus.
Network-layer threat intelligence Many attacks can be intercepted before they reach endpoints or applications — at the network level, through DNS and infrastructure telemetry. We help organisations use this layer of visibility to detect malicious activity early and block threats proactively, turning the network itself into a preemptive control.
The outcome
Organisations that invest in preemptive security face incidents less frequently, limit the blast radius when something does occur, and can demonstrate to leadership and regulators that their posture is grounded in evidence rather than assumption.
In an era where AI is amplifying attacker capabilities, the shift from reactive to preemptive is no longer a long-term ambition. It is an operational necessity.
Do you want to know more about this topic?
Our experts and sales teams are at your service. Leave your contact information and we will get back to you shortly.