Cybersecurity is a battleground, and as the digital landscape evolves, so do the tactics of malicious actors. One strategy to fortify your defences and identify vulnerabilities is the practice of red teaming.
Red teaming is vital for organisations as it realistically simulates cyber threats, offering a full evaluation of security across technology, human resources, and infrastructure. It identifies weaknesses, tests incident response, and prepares for advanced attacks, enabling ongoing improvement and learning between internal defenders and simulated adversaries. The insights gained support strategic decision-making, ensuring organisations stay resilient against evolving cyber threats.
In this article, we'll explore red teaming, its benefits, the steps involved, and continuous automated red teaming.
What is a red team?
In cybersecurity, a red team is not just a group of experts; it strategically mimics the tactics of real cyber adversaries to assess an organisation's resilience. Originating from military simulations, red teaming has become crucial for organisations defending against various cyber threats. Consisting of highly skilled cybersecurity professionals, the red team operates independently, often hired externally for an unbiased evaluation.
The red team's primary goal is to authentically simulate real-world cyber threats. It employs diverse tactics, mirroring malicious actors' methodologies, from social engineering and phishing to exploiting technology vulnerabilities and probing physical security. Unlike penetration testing, red team exercises are conducted without warning to the internal security team, ensuring a genuine measure of the organisation's ability to respond to a surprise cyber-attack.
At its core, a red team serves as a simulated adversarial force, relentlessly testing an organisation's security posture. By adopting external threat actors' mindset, the red team provides invaluable insights into identifying vulnerabilities and evaluating an organisation's response capabilities.
Benefits of red teaming
Why subject your organisation to red team testing? The benefits are many. This approach offers a comprehensive assessment of your cybersecurity, providing insights into vulnerabilities across various domains. Red teaming goes beyond technology, scrutinising human resources and infrastructure vulnerabilities, and preparing your defense team for real-world scenarios.
- Holistic security assessment: It provides a comprehensive evaluation of cybersecurity by simulating real-world threats, including social engineering and physical security, offering a realistic view of vulnerabilities.
- Identification of vulnerabilities: It uncovers both technical and non-technical vulnerabilities, offering organisations insights into weaknesses in technology, human resources, and infrastructure.
- Testing incident response: Red team testing evaluates incident response procedures, challenging the internal security team (blue team) to detect and respond to simulated cyber threats, identifying and improving response capabilities.
- Realistic threat scenarios: It emulates advanced persistent threats (APTs), providing a realistic threat scenario that enhances organisations' understanding of their security posture against sophisticated cyber attacks.
Understanding the differences: Red team, blue team, and purple team
In cybersecurity, specialised teams collaborate to fortify an organisation's defences. Let's explore the characteristics of red teams, blue teams, and the collaborative purple team approach.
Red team
The red team acts as a simulated adversary, executing sophisticated cyber-attacks to identify vulnerabilities within an organisation's security infrastructure. Comprising skilled security professionals, the red team conducts independent assessments, emulating real-world threats without the blue team's knowledge.
Blue team
In contrast, the blue team serves as the organisation's internal defender, responsible for protecting networks, systems, and applications. Unaware of red team simulations, the blue team monitors, detects, and responds to simulated attacks, showcasing real-time defensive capabilities.
Purple team
The purple team bridges the gap between red and blue teams, fostering collaboration for a more holistic security approach. In scenarios where the blue team is informed about red team simulations, they work together in a purple team setup. This cooperative mindset encourages efficient communication and knowledge-sharing between offensive and defensive security teams, enhancing overall cybersecurity resilience.
How does a red team work?
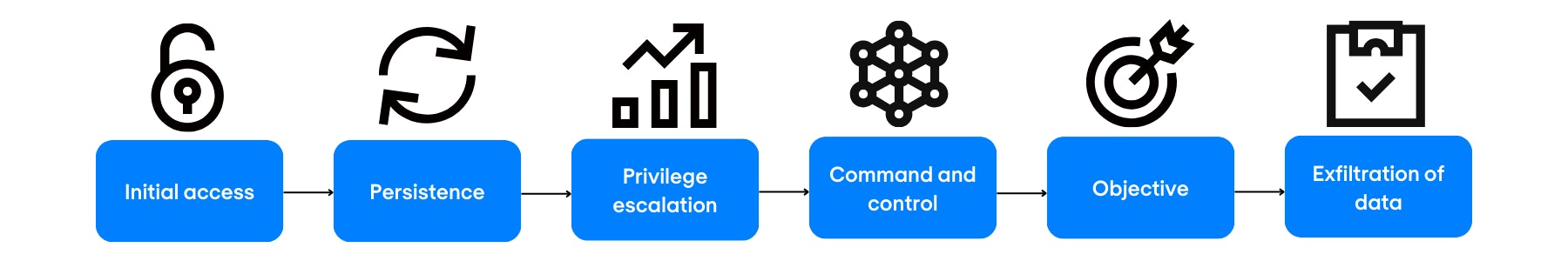
Red teaming involves a strategic and methodical approach to simulate real-world cyber threats. The process typically follows a chain of stages, including initial access, persistence, privilege escalation, command and control, objective attainment, and data exfiltration. Drawing inspiration from threat intelligence reports or current trends, the red team emulates specific threat actors, adapting their tactics, techniques, and procedures (TTPs) to the organisation's context.
During an engagement, the red team operates to access predetermined targets, such as sensitive data or critical systems. This involves employing various tactics, including social engineering, application penetration testing, network sniffing, and physical security testing. The blue team, unaware of the ongoing simulation, is tasked with defending the organisation against these simulated attacks. This dynamic interaction allows both teams to learn from each other, with the red team revealing vulnerabilities and the blue team honing its detection and response capabilities. The ultimate goal is to provide organisations with actionable insights into their cybersecurity posture and enhance their ability to thwart sophisticated cyber threats.
Red teaming in OT
Red teaming in Operational Technology (OT) environments is a specialised practice aimed at assessing the security posture of critical infrastructure, industrial control systems (ICS), and other OT assets. OT environments, which include sectors like energy, manufacturing, and utilities, face unique challenges due to their interconnected nature and reliance on industrial control systems.
Within OT red teaming, the focus extends beyond traditional cybersecurity assessments. It involves simulating sophisticated cyber-attacks on OT systems, such as Supervisory Control and Data Acquisition (SCADA) systems, programmable logic controllers (PLCs), and other components crucial to industrial processes. The goal is to identify vulnerabilities, evaluate the resilience of OT security defences, and enhance the overall cybersecurity posture.
Continuous Automated Red Teaming (CART)
Continuous Automated Red Teaming (CART) emerges as a cutting-edge approach in the realm of cybersecurity, revolutionising how organisations fortify their digital defences. In the ever-evolving landscape of cyber threats, CART offers a proactive and automated solution to keep pace with adversaries' tactics, ensuring a constant and dynamic evaluation of an organisation's security infrastructure.
CART leverages automated tools and sophisticated technologies to simulate persistent cyber threats continuously. Unlike traditional red teaming, which operates periodically, CART provides an ongoing assessment, enabling organisations to adapt swiftly to emerging risks. This approach aligns with the prevailing philosophy that cybersecurity is not a one-time event but a continuous process of refinement and enhancement. By integrating CART into their cybersecurity strategy, businesses can establish a resilient defence mechanism that remains agile and responsive in the face of evolving threats, ultimately fortifying their digital landscapes against potential breaches.
The next step
Embarking on a red teaming exercise goes beyond a routine security evaluation; it's a strategic initiative to strengthen your organisation's cyber resilience. As you uncover vulnerabilities and enhance your understanding of potential threats, the insights gained become invaluable for shaping targeted security improvements.
At Nomios, we understand the strategic importance of these insights. Leveraging our proficiency in red teaming and a diverse range of cybersecurity solutions, we stand ready to guide you in fortifying your organisation's digital landscape. If you're eager to explore how Nomios can customise a security solution tailored to your specific needs, we invite you to connect with us. Take the next step towards building robust cybersecurity defences and ensuring the ongoing security posture of your organisation.
Our team is ready for you
Do you want to know more about this topic? Leave a message or your number and we'll call you back. We are looking forward to helping you further.