
Artificial Intelligence
The coming patch tsunami: how AI is rewriting the vulnerability landscape
AI systems are finding vulnerabilities. Not incidentally, but at a scale and pace that is putting the traditional vulnerability chain under strain.

Richard Landman


Artificial Intelligence
Koi and the Palo Alto Networks acquisition: agentic endpoint security becomes a category of its own
As a child, I used to fish for carp in the park pond in Voorschoten. Waiting patiently, watching for the float to move, hoping you'd spot it in time. Those carp are called koi in Japanese — a symbol of perseverance and attentiveness.

Richard Landman


Preemptive Security
Attacks start outside your network. So should your security.
Phishing pages, fake executive profiles, leaked credentials on the dark web – most attacks take shape long before they reach your network. Yet traditional security largely focuses on what happens after that boundary. Infoblox is taking a different approach.

Michel Geensen

Quantum Security PKI
Preparing PKI for the post-quantum transition
PKI is one of the most complex parts of the post-quantum transition. Learn why certificate infrastructure requires early planning and what your organisation should focus on now.

Priyanka Gahilot


MDR
Nomios launches Guardian xMDR: enterprise-grade managed detection and response
Our new standardised MDR service combines Cortex XDR, a Dutch SOC, and transparent tier-based pricing — so organisations of every size can take managed security seriously.


Artificial Intelligence
Project Glasswing: when AI finds vulnerabilities that lay hidden for thirty years
Anthropic has launched Project Glasswing together with a coalition of twelve leading technology and security companies.

Richard Landman

Digital Sovereignty
My data is stored in Europe — so what could possibly go wrong?
The question sounds almost rhetorical: if my data resides in a data centre in Amsterdam or Frankfurt, surely I meet all requirements?
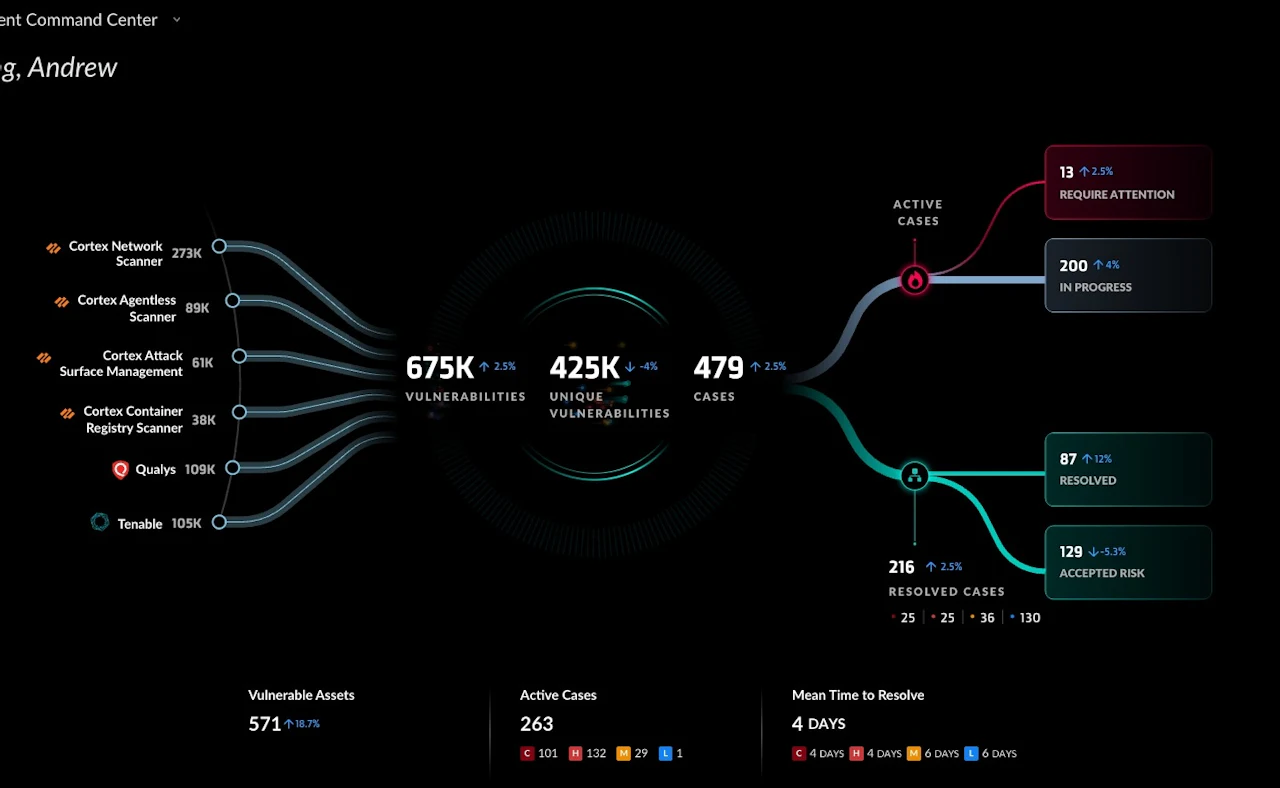

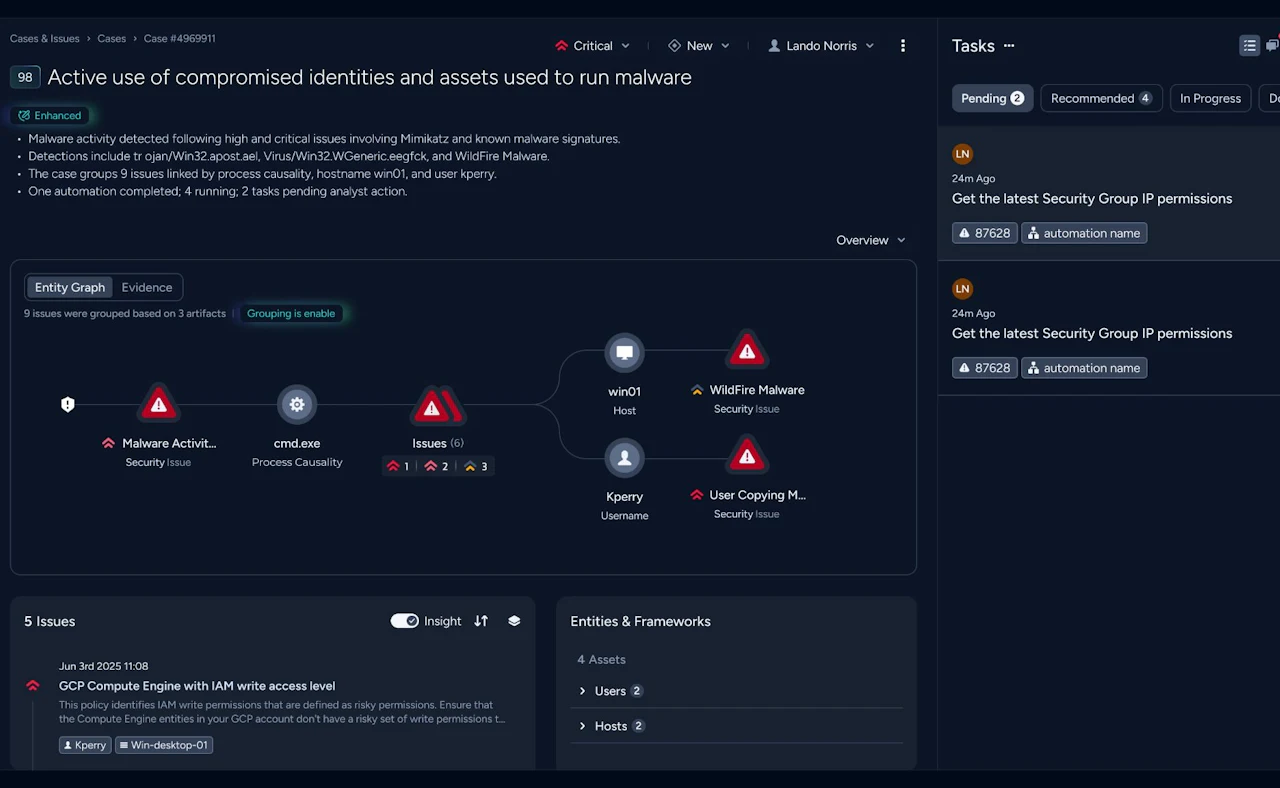
XDR
Palo Alto Networks launches Cortex XDR 5.0: ready for the next step in security operations?
Attackers are moving faster than ever. The time between initial access and full compromise has shrunk to minutes — and more than 90% of all breaches can be traced back to preventable gaps.

Richard Landman


MDR Assume Breach
Assume breach in practice: what it really demands of your security team
The NCSC recently published a practical guide for security professionals: Convince your board of assume breach.

Bas de Mooij


DDI
Nomios achieves Infoblox's highest partner status — as the only European integrator
Nomios Group has achieved Diamond partner status with Infoblox, the highest tier within the Infoblox partner network.

SIEM MDR
Cortex XDR as SIEM light: powerful detection and compliance without the complexity
Many organisations face the same dilemma: they know they need better visibility into what is happening across their environment, but a full SIEM platform feels like a significant undertaking — expensive, complex to manage, and heavy to implement.

Richard Landman


Quantum Security Network security
Why quantum-safe networking needs to be on your agenda
Find out why quantum-safe networking should be on every IT leader's agenda and what practical steps to take now on encryption, key governance, and post-quantum cryptography readiness.

Vincent de Knegt

SOC
The data layer as the foundation of the modern SOC
Anyone building or modernising a Security Operations Centre will eventually reach the same conclusion: the quality of the data layer determines the quality of everything built on top of it.

Richard Landman


SASE
FortiOS 8.0: Secure Networking in the AI Era
At Fortinet Accelerate 2026 in Las Vegas, Fortinet introduced FortiOS 8.0, the latest release of the operating system powering the Fortinet Security Fabric.

Michel Adelaar


NGFW
Security from Core to Edge: HPE Juniper Networks Introduces the SRX400 Series
One of the most concrete announcements is the HPE Juniper Networking SRX400 series: a compact next-generation firewall that brings carrier-grade security to the edge of the network.

Richard Landman


Digital Sovereignty
Digital Sovereignty That Works in Practice: Local Control, Global Resilience
Zscaler introduces the expansion of its digital sovereignty capabilities.

Richard Landman

Identity
Nomios, Intragen and CyberArk: Identity Security as an Accelerator for Zero Trust
Identity Security as the Engine of Zero Trust: A “Match Made in Heaven” Between CyberArk and Palo Alto.

Richard Landman


Data centre Quantum Security
Quantum-safe networking design patterns for the data centre fabric and DCI
Practical guidance for applying multi-layer encryption, preparing the management plane for PQC, and building crypto-agility into your data centre fabric and DCI architecture.

Vincent de Knegt
Sign up for our newsletter
Get the latest security news, insights and market trends delivered to your inbox.







